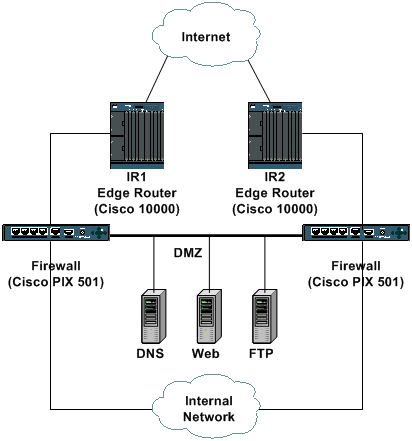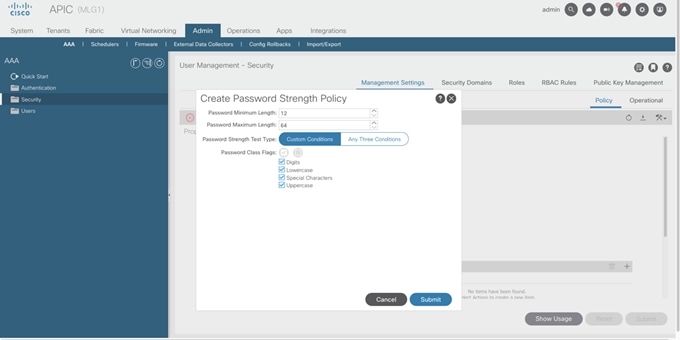
PDF) Hardening CISCO Devices based on Cryptography and Security Protocols - Part II: Implementation and Evaluation

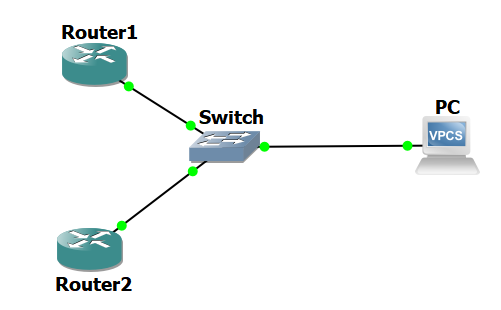
Ch6: PT Activity 4 - Device Hardening: Objective | PDF | Router (Computing) | Command Line Interface

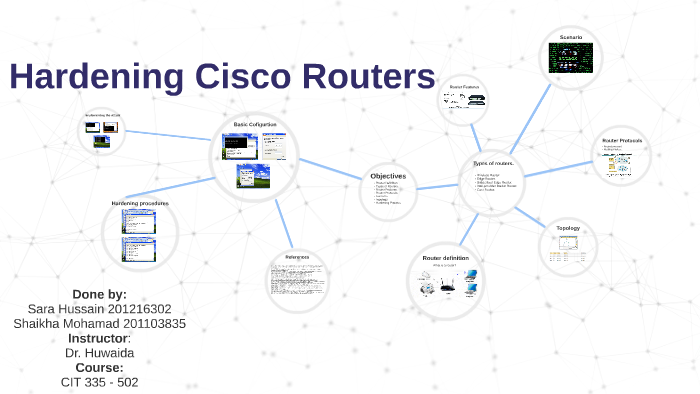
Cisco Router/Switch Hardening Southern Colorado Cisco Users Group April 14, 2003 William H. Gilmore | Scott R. Hogg International Network Services. - ppt download
![Cisco Catalyst IR1101 Rugged Series Router Software Configuration Guide - Introduction [Cisco Catalyst IR1100 Rugged Series Routers] - Cisco Cisco Catalyst IR1101 Rugged Series Router Software Configuration Guide - Introduction [Cisco Catalyst IR1100 Rugged Series Routers] - Cisco](https://www.cisco.com/c/dam/en/us/td/i/400001-500000/420001-430000/428001-429000/428004.jpg)
Cisco Catalyst IR1101 Rugged Series Router Software Configuration Guide - Introduction [Cisco Catalyst IR1100 Rugged Series Routers] - Cisco

PDF) Hardening CISCO Devices based on Cryptography and Security Protocols - Part II: Implementation and Evaluation
![Cisco Catalyst IR1101 Rugged Series Router Software Configuration Guide - Introduction [Cisco Catalyst IR1100 Rugged Series Routers] - Cisco Cisco Catalyst IR1101 Rugged Series Router Software Configuration Guide - Introduction [Cisco Catalyst IR1100 Rugged Series Routers] - Cisco](https://www.cisco.com/c/dam/en/us/td/i/400001-500000/460001-470000/461001-462000/461414.jpg)
Cisco Catalyst IR1101 Rugged Series Router Software Configuration Guide - Introduction [Cisco Catalyst IR1100 Rugged Series Routers] - Cisco

Security Sage's Guide to Hardening the Network Infrastructure: Andres, Steven, Kenyon, Brian, Pack Birkholz, Erik: 9781931836012: Amazon.com: Books

Ch6: PT Activity 4 - Device Hardening: Objective | PDF | Router (Computing) | Command Line Interface
CCNA Routing and Switching Portable Command Guide (ICND1 100-105, ICND2 200-105, and CCNA 200-125), 4th Edition | Cisco Press